Introduction: Assessing Cybersecurity Risks and Defence Strategies for Industry 4.0
The report is done to evaluate the major principles of security which are prevalent in small and medium-sized enterprises. The majority of the issues are occurring because of the need to update the dataset based on the change in times. With growing times the customer database is very essential to be updated to cater the new and recent offers and information to the customer base of the company. The servers that are used by the companies are all legacy systems which are all outdated and because of this, there are many trojans and other malware which affect the performance of the systems and their servers. The company LiveWell is selected in this case study to evaluate and analyse several principles that are majorly responsible for the risks to the cyber security of the companies.
Explore unparalleled assignment help UK with Native Assignment Help. Our commitment to quality and customer satisfaction sets us apart, making us the preferred choice for students seeking reliable assistance.
Cybersecurity
1.1 Assumptions
There are a few factors which can be assumed in this case study to evaluate the factors which hamper the security of the company LiveWell. The market position of the company is in a fluctuation phase where there are a constant influx of newer customers but the database and the supporting systems of the company are not able to provide smooth service to the customers and there are anomalies generated as a result of the malware which is posing great threats to the company to retain the market position and the customer base of the company. The skills of the staff of the company are also not up to the mark for a smooth service and satisfied service for the customers. The company LiveWell is one of the moderate-sized startups in the market and is running functionally to provide physiotherapy services to patients since the company is a start-up, therefore, these threats can be very serious for the establishment of the company in the market and within customers.
1.2 Risk Identification
There are certain risks associated with the performance of the company which can bring severe threats to the position and the working of the company and the services which are received by the patients and customers of the company LiveWell. Some risks are identified, such as
- Vulnerabilities identified: Some vulnerabilities are present in the company because of the prevalent threats to the functioning and purpose of the company. The threat such as the lack of functional and management skills of the staff is one of the prime reasons for the uneven and improper distribution of responsibilities and duties. Proper steps to safeguard the information of the database of the company are one serious threat which can cause serious problems for the company in the market. Because of the system gap, there are threats or vulnerabilities which can occur due to virus attacks in the centralised database of the company, the present and the potential customers are being served anomalous information regarding offers and policies of the company and because of this, the data of the customers of the company in the databases are all corrupted.
- Threats Identified: There is a massive gap between the staff and this is one of the reasons for the improper fulfilment of duties and responsibilities. The gap in technology is also present in the organization and this is because of the use of the legacy systems in their systems and because of the uneven division of responsibilities and staff (Akinrolabu et al. 2019). The information which is essential for the company is stored in the database of the company, the company has used a new means to manage the data of the customers which is the use of dedicated web portals which are connected to the database of the company. In present times the company is gaining an improved position in the market and because of this, the influx of customer data in the systems of the company LiveWell is increasing therefore the database and the data of potential and old customers are prone to malware attacks. The staff of the company need to be appropriately skilled to handle the issues which the company faces in the collection of customer data from the market.
Risk Management
2.1 Weighted Factor Table
The weighted factor table is built according to the threats and vulnerabilities mentioned in this research. The threats are evaluated and the vulnerabilities that are caused due to the threats are also analysed and the weights are given according to the impact posed by the threats to the organisation (Lyu et al. 2019). The assets which are considered to be affected by risks are analysed and their values are evaluated in this table.
| Information Asset | Impact on revenue | Impact on profitability | Impact on Cyber Security | Weighted Score |
| Criterion Weight (1-100) | 30 | 30 | 40 | 100 |
| Human Resource | 15 | 15 | 30 | 60 |
| Skills of staff | 25 | 25 | 30 | 80 |
| Efficient distribution of responsibilities | 15 | 20 | 25 | 60 |
| Implementation of strong security parameters | 25 | 30 | 40 | 95 |
Table 1: Weighted Factor Table
The factors are given weightage according to the priority and the impact of the factors on the functional parameters of the company and the assets of the company LiveWell. The factor of lack of staff and insufficient skills of the employees are one of the least weighted parameters as these factors can be easily enhanced and the effects that are posed by these factors are not very severe to the organisation (Tantawy et al. 2020). Factors such as the efficient distribution of dedicated tasks and responsibilities are posing a threat to the company because of inefficient management and because of legacy systems to maintain the database of the companies. The impact that is posed by the factors on the performance of the organisation is measured and then weighted in the table above to evaluate clearly the factors of threats for the organisation.
2.2 Risk Register

Figure 1: Risks of the company
The risks that are associated with the factors of distress for the startup company LiveWell are accounted for in the risk register table where the risks are rated and evaluated. The nature of the threats is evaluated and the stage of the business cycle where the error occurs is specified along with the standard of importance the threat is for the organisation (Süzen. 2020). The risk register is provided below to provide a matrix of the threats and the impacts of the threats that are posed to the organisation in an unsorted manner.
| ID | Value | Risk | Impact on revenue | Impact on profitability | Impact on Cyber Security | Likelihood of The Risk Happening | Nature of the risk |
| 1 | 60 | Lack of enough staff | The company is a start-up and the lack of human resources is a serious threat to the company to growth in the market. | Human resources are essential units to bring in profit for the company. | The customer base of the company is increasing but the human resources of the company are not enough to ensure cyber security to the essential data of the customers | The risk of low human resources is one of the risks prevalent in the company LiveWell | This is a production risk, which means this issue occurs and hampers the production phase. |
| 2 | 80 | Lack of strong skills | The skills of the employees of the company are essential for the influx of high revenue for the company. | Profits of the company are earned when the employee complete their dedicated tasks with proper execution of quality skills. | The skills of the employees are very essential to enhance the cyber security of employees there are no prevalent methods of cyber security in the company. | The skills of the staff hired by the company are not efficient to handle complex problems which are essential to ensure the safety of customer data. | This kind of threat arises in the management phase of the business cycle. |
| 3 | 60 | Uneven distribution of responsibilities | When the dedicated responsibilities are being distributed unevenly then the revenue that is earned by the company is affected severely. | The profit that is earned by the company reduces when the responsibilities are not properly distributed among the employees. | The security of the essential data of the potential and the old customers of the company is being affected by the weak management as only one database is responsible for accounting for the data collected from the patients. | Responsibilities are not distributed evenly in the company and this is one of the reasons for all the problems to create vulnerability in the working of the company. | This kind of risk primarily occurs in the management phase where the responsibilities and duties of the employees are being done. |
| 4 | 95 | Inefficient cyber security measures | The essential data of the details of the potential and old customers are not secured in the database using efficient cyber security measures, the databases are affected by virus attacks and this is one serious threat for the revenue earned by the company as it hampers customer satisfaction and company image. | The profitability of the company is low because of inefficient cyber security of the customer data because of the growing customers of the company in the market. | The data of the customers are being saved in the database of the company, but because of inefficient cyber protection techniques, there are attacks of viruses on the database which can hamper the smooth functioning of the business. | The company has inefficient methods for ensuring cyber protection and as a result, the customers received anomalous information regarding promotions and policies of the company. | This kind of risk primarily occurs in the operation phase where the process or the core operation of the business runs. |
Table 2: Risk Register (non-prioritized)
2.3 Prioritised Risk Register
The risk register that is formed with the help of the evaluation of the risks associated with the organisation of LiveWell is prioritised based on the values that are weighted against each of the factors and the vulnerability which is brought down because of the threats in the working of the company. The sorted risk register is provided below which is prioritised with the help of colour. The entire information regarding the risks is provided in the risk register, and the severity and priority of the risk are denoted and evaluated with the help of colours where red is the colour chosen to represent high parameters green represents low parameters and yellow is used to denote moderate parameters.
| Risk | Value | Management | Operation | Security | Reason |
| Inefficient cyber security measures | 95 | Medium | High | High | The company LiveWell is taking insufficient measures to ensure cyber security. The impact of the risk on management is medium since the security of the cyber networks does not affect the management and is of high priority in case of operation and security since the security of the cyber links is associated greatly with the normal operations of the company and the security of the customer data. |
| Lack of strong skills | 80 | Low | High | Medium | The relevant skills of the people should be enhanced so that the processes can be smooth and hence it is of high priority in the domain of operations but is of medium priority in the case of security and low in the case of management in the company. |
| Uneven distribution of responsibilities | 60 | High | Medium | Low | Responsibilities should be divided in an equal manner in the company for the smooth running of processes. Therefore the priority of the risk is high in the domain of management but is of medium priority in the domain of operation and low in the case of security. |
| Lack of enough staff | 60 | Medium | Medium | Low | Human resources is not the most important risk for any organisation, the lack of human resources is of medium priority for the domain of management and operation of the company but is of low priority in the case of security. |
Table 3: Prioritised Risk Register
Risk Control
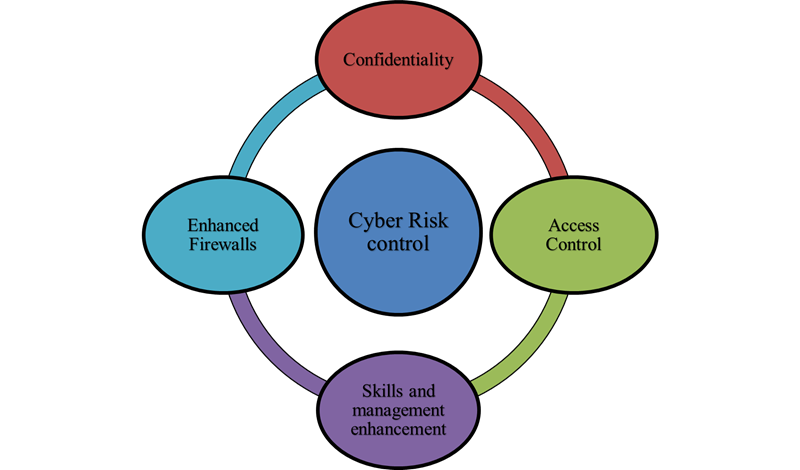
Figure 2: Cyber Risk Control
The risks that are identified in the company LiveWell are evaluated with the help of the risk register where the weightage of the risks is provided according to the impacts posed by the risks on the working and processing of the company. In present times there is a huge influx of the customer base of the company of active marketing of the services of the company. Because of this increase in customer data, the company has used several web portals to increase the access of the company to the customer database (Tam. 2019). The database which collects customer information from the market is just one central database and because of this, any attack of viruses or any risk of cyber links can affect the central customer database of the company. A case study of the company LiveWell is selected where the customers of the company have received malicious information regarding the promotions and offers of the company because of the virus attack on the database which has corrupted the data of the databases. The cyber strength of the cyber links of the company can be enhanced with the help of many techniques such as
- Enhancement of Confidentiality- LiveWell uses an appropriate system of confidential systems where the login is done but the strength of the confidentiality can be increased with the use of better confidential data key pairs. The confidential systems of organisations accept a unique key as its only key to get opened and hence a strong and confidential system can be an essential and functional solution to the problem of cyber security of the company. Access to a particular data can be only possible only with the provision of a unique key. Customer data is a very essential information which can be used for many purposes by the company and therefore the privacy of customer data is very essential.
- Enhanced Firewalls- Firewalls can be used to protect the data from cyber-attacks of unauthorised data access or from malicious viruses which can corrupt the essential data of the companies. There are systems which automatically activate a layer of antivirus and protective firewall when the system gets any signal malfunctioning due to a virus attack (Zografopoulos. 2020). Firewalls also let the company know exactly when the attack will take place which can be a precursor to safeguard the data of the company. There are systems where multiple layers of firewalls protect severely information from being corrupted by external means.
- Access Control- The major problem of the company LiveWell is the use of legacy systems in the database of the company. The rising data of the customers that are gathered by the company from the market are being stored in the central database which is accessed by some admin teams but the teams are not specified about their responsibility this causes the rise of malware as the database is accessed by multiple people from multiple locations but the access limits of the users can be specified by the admin in the system. The limits of access mean the users will have a limit on the editing, entry and updating of the data collected from the market. With the help of the access control principle in cyber security, the access of the users can be controlled by the admin of the system.
- Skills and management enhancement- The skills of the employees in the company are not enough for the growth of the company in the growing market. The company is a startup with about 50 members in their team, the team needs to be increased so that dedicated people can be allocated their respective tasks which can be fulfilled smoothly. The management of the company should be made better so that no anomalies can arise in the access of the data for providing customer information to the company. Extensive measures to enhance the skills of the employee can bring smoothness in the operations of the company and also reduce the chances of risks in the security of the data.
Conclusion
The report is done to evaluate the principle of security of the organisation in matters of cyber security. A case study is chosen and the company LiveWell is chosen which a company is working in the domain of physiotherapy, and customer base of the company is facing a rise in the present times because of the extensive marketing of the company. Several factors which are factors of distress are identified in the company and the risks associated with the processes are analysed with proper evaluation of the vulnerabilities which occur because of the risks in the organisation. The techniques which can be used to manage the risks are also provided in the report, to ensure the security of the customer data collected by the company from the market. The data of the database of the company are very essential as these data bring essential decisions for the company and it is very important for a rising company like LiveWell to maintain the authenticity and the privacy of the customer data.
References
Book
Francesco Flammini (2019). Resilience of Cyber-Physical Systems. Available at- https://link.springer.com/book/10.1007/978-3-319-95597-1. [Accessed on 15.02.2023]
Journals
Akinrolabu, O., Nurse, J.R., Martin, A. and New, S., 2019. Cyber risk assessment in cloud provider environments: Current models and future needs.Computers & Security,87, p.101600.
Amin, Z.M., Anwar, N., Shoid, M.S.M. and Samuri, S., 2022. Method for Conducting Systematic Literature Review (SLR) for Cyber Risk Assessment.Environment-Behaviour Proceedings Journal,7(SI10), pp.255-260.
Chang, C.H., Kontovas, C., Yu, Q. and Yang, Z., 2021. Risk assessment of the operations of maritime autonomous surface ships.Reliability Engineering & System Safety,207, p.107324.
Dai, Q., Shi, L. and Ni, Y., 2019. Risk assessment for cyberattack in active distribution systems considering the role of feeder automation.IEEE Transactions on Power Systems,34(4), pp.3230-3240.
Ganin, A.A., Quach, P., Panwar, M., Collier, Z.A., Keisler, J.M., Marchese, D. and Linkov, I., 2020. Multicriteria decision framework for cybersecurity risk assessment and management.Risk Analysis,40(1), pp.183-199.
Kalinin, M., Krundyshev, V. and Zegzhda, P., 2021. Cybersecurity risk assessment in smart city infrastructures.Machines,9(4), p.78.
Lyu, X., Ding, Y. and Yang, S.H., 2019. Safety and security risk assessment in cyber‐physical systems.IET Cyber‐Physical Systems: Theory & Applications,4(3), pp.221-232.
Tantawy, A., Abdelwahed, S., Erradi, A. and Shaban, K., 2020. Model-based risk assessment for cyber physical systems security.Computers & Security,96, p.101864.
Milošević, J., Sandberg, H. and Johansson, K.H., 2019. Estimating the impact of cyber-attack strategies for stochastic networked control systems.IEEE Transactions on Control of Network Systems,7(2), pp.747-757.
Mokhor, V., Gonchar, S. and Dybach, О., 2019. Methods for the total risk assessment of cybersecurity of critical infrastructure facilities.Ядерна та радіаційна безпека, (2 (82)), pp.4-8.
Nifakos, S., Chandramouli, K., Nikolaou, C.K., Papachristou, P., Koch, S., Panaousis, E. and Bonacina, S., 2021. Influence of human factors on cyber security within healthcare organisations: A systematic review.Sensors,21(15), p.5119.
Riesco, R. and Villagrá, V.A., 2019. Leveraging cyber threat intelligence for a dynamic risk framework: Automation by using a semantic reasoner and a new combination of standards (STIX™, SWRL and OWL).International Journal of Information Security,18(6), pp.715-739.
Rosati, P., Gogolin, F. and Lynn, T., 2019. Audit firm assessments of cyber-security risk: evidence from audit fees and SEC comment letters.The International Journal of Accounting,54(03), p.1950013.
Sardi, A., Rizzi, A., Sorano, E. and Guerrieri, A., 2020. Cyber risk in health facilities: A systematic literature review.Sustainability,12(17), p.7002.
Süzen, A.A., 2020. A Risk-Assessment of Cyber Attacks and Defense Strategies in Industry 4.0 Ecosystem.International Journal of Computer Network & Information Security,12(1).
Tam, K. and Jones, K., 2019. MaCRA: a model-based framework for maritime cyber-risk assessment.WMU Journal of Maritime Affairs,18, pp.129-163.
Zografopoulos, I., Ospina, J., Liu, X. and Konstantinou, C., 2021. Cyber-physical energy systems security: Threat modeling, risk assessment, resources, metrics, and case studies.IEEE Access,9, pp.29775-29818.